Security Development Tools
When a design needs secure identity, protected key storage, trusted boot support, or device authentication, the development phase usually starts with practical evaluation hardware. Security Development Tools help engineers test secure elements, authenticators, TPM platforms, and reference implementations before moving into production hardware. For embedded systems, automotive electronics, industrial IoT, and connected edge devices, these tools make it easier to validate both hardware integration and the broader security architecture.

Where these tools fit in an embedded security workflow
Security is rarely a single component decision. In practice, engineering teams often need to evaluate how a secure element, authenticator, or TPM behaves alongside the host MCU, firmware, communication interface, and provisioning flow. Development kits and evaluation boards reduce that risk by providing a faster path to proof-of-concept work, interoperability checks, and early software development.
This category is especially relevant for projects involving device authentication, secure credential storage, anti-counterfeiting measures, protected communications, and platform trust. Some tools are aimed at board-level experiments, while others are better suited for application-focused validation such as automotive nodes, Raspberry Pi-based gateways, or Arduino-compatible prototyping.
Typical product types in this category
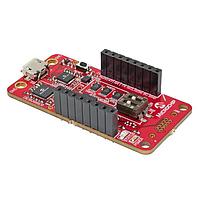
The range of security development hardware can include evaluation kits, breakout boards, reference designs, and platform-specific starter boards. Each format serves a different purpose. Evaluation kits usually focus on a specific security IC, while reference designs can show how the device fits into a broader implementation with interfaces, host processors, and firmware examples.
For example, the NXP OM-SE050ARD-E development kit is positioned around the EdgeLock SE050E and is useful for teams exploring secure element integration in an Arduino-compatible environment. On the other hand, a board such as the Infineon TPM9672FW1613RPIEBTOBO1 provides a more direct route for working with a TPM on Raspberry Pi-based platforms, which can be valuable for gateway, edge computing, or trusted platform experiments.
Breakout-style options also have a place in early design work. The Adafruit 4314 ATECC608 breakout board, for instance, is suited to fast bench evaluation where engineers want straightforward access to an I2C-based security device during firmware bring-up or prototype testing.
Interfaces and integration considerations
One of the first selection criteria is the host interface. In this category, common interfaces shown in representative products include I2C, 1-Wire, USB, and SPI. The right choice depends on the target system, available MCU resources, firmware maturity, and how the secure device will be used in the final design.
I2C-based tools can be convenient for compact embedded designs and quick integration with development boards. 1-Wire options may be attractive in authentication-focused applications where wiring simplicity matters. USB-connected evaluation hardware can speed up testing on the bench, while SPI-based TPM platforms are often relevant when the goal is platform trust, protected boot chains, or host processor security.
If your project also involves broader connectivity testing, it can be helpful to review related communication development tools alongside the security evaluation setup, especially when authentication and secure data exchange are being validated together.
Representative platforms and manufacturers
Several well-known suppliers appear in this category, including Analog Devices, NXP, Infineon, and Adafruit. The available tools reflect different security approaches, from secure authenticators and secure elements to TPM-based evaluation. Rather than choosing by brand alone, it is usually better to match the tool to the intended trust model, software stack, and host environment.
Within the Analog Devices range, examples such as the DS28E38EVKIT#, DS28C40EVKIT#, and DS28C39EVKIT# illustrate evaluation paths for secure authentication devices over interfaces such as 1-Wire or I2C. The MAXREFDES143# reference design is also notable because it gives useful context for an embedded security reference design rather than a bare-device-only evaluation flow. For engineers comparing secure hardware concepts across vendors, the NXP ecosystem is also relevant where secure element evaluation is part of a broader connected product strategy.
How to choose the right security development tool
A practical starting point is to define the security function clearly. Some projects need secure key storage and cryptographic operations in a compact peripheral device. Others need anti-cloning features, accessory authentication, or a TPM-oriented root of trust for a Linux-capable host. Once that purpose is clear, it becomes easier to narrow down the right board or kit.
It is also important to check the intended evaluation target and development environment. Tools built for a specific device family are best when your component choice is already known. More open-ended boards can be better for learning, early architecture work, or software prototyping. Supply voltage, host interface, and platform compatibility all matter, but in many cases the deciding factor is how quickly the tool lets your team test real security workflows such as provisioning, credential handling, challenge-response authentication, or trust establishment.
- Choose by security goal: secure element, authenticator, TPM, or reference design validation.
- Choose by interface: I2C, SPI, 1-Wire, or USB depending on the host system.
- Choose by platform fit: Arduino-compatible, Raspberry Pi-compatible, or bench evaluation.
- Choose by workflow: standalone IC testing, firmware integration, or full system prototyping.
Use cases across industrial, automotive, and IoT projects
These tools are often used early in programs where security must be designed in rather than added later. In industrial and IoT applications, engineers may evaluate secure authentication for sensors, edge nodes, accessories, or field-replaceable modules. In automotive-related work, the focus may shift toward protected communication, ECU identity, accessory validation, or trusted subsystem design.
Some representative products in this category point to those use cases directly. The DS28C40EVKIT# is associated with an automotive I2C authenticator evaluation path, while the Adafruit 3363 FIDO2 U2F security key highlights another side of the category: hands-on development around user-facing authentication and modern security token concepts. That makes the category relevant not only for chip-level design teams, but also for engineers building demos, validation systems, and proof-of-concept platforms.
Related development areas worth exploring
Security evaluation does not happen in isolation. In many embedded projects, it overlaps with memory, communication, and system integration work. If your design includes protected storage, secure boot assets, or firmware credential handling, reviewing memory IC development tools may help provide additional context during architecture planning.
For teams building complete prototypes, it can also be useful to combine security boards with suitable processor, sensor, or interface hardware from suppliers such as Adafruit. That approach is often valuable in fast-turn prototype environments where engineers need to move quickly from device evaluation to application-level testing.
Finding the right starting point
The best choice depends less on the number of features on a board and more on how closely it matches the security task you need to validate. A compact breakout may be enough for firmware learning and interface checks, while a dedicated evaluation system or reference design can be more appropriate when the goal is to assess trust architecture, host integration, or deployment flow.
By comparing interface options, target devices, and platform compatibility, engineers can use this category to shorten evaluation time and make more confident design decisions. Whether you are exploring secure authenticators, TPM-based trust anchors, or secure element integration for embedded products, this selection of security development hardware provides a practical foundation for moving from concept to implementation.
Get exclusive volume discounts, bulk pricing updates, and new product alerts delivered directly to your inbox.
By subscribing, you agree to our Terms of Service and Privacy Policy.
Direct access to our certified experts